How live assist prevents accidental PHI disclosure during calls
-
Bella Williams
- 10 min read
In today's highly regulated environment, contact centers face the constant challenge of protecting sensitive information, particularly Protected Health Information (PHI) in healthcare settings. Accidental disclosures can lead to severe consequences, including hefty fines, legal repercussions, and damage to reputation. The stakes are high, and organizations must implement robust measures to safeguard patient data during calls. This is where live assist technology comes into play, offering a proactive solution to prevent accidental PHI disclosures.
Understanding Compliance Risk in Contact Centers
The High-Stakes Regulatory Environment:
Contact centers operate under stringent regulations, particularly in healthcare, where HIPAA governs the protection of patient information. Violations can result in significant financial penalties, with HIPAA fines ranging from $100 to $50,000 per violation, depending on the severity and frequency of the offense. Beyond direct financial implications, non-compliance can lead to reputational damage, loss of customer trust, and operational restrictions.
The Cost of Non-Compliance:
Direct Financial Impact:
- HIPAA violations: $100 – $50,000 per violation (up to $1.5 million annual maximum)
- Potential class action lawsuit exposure: millions in damages
Indirect Business Impact:
- Regulatory investigations can incur legal fees and audit expenses.
- Business interruptions due to consent decrees can lead to operational restrictions.
- Loss of reputation can result in customer attrition and decreased revenue.
Why Traditional Compliance Monitoring Fails
Traditional compliance monitoring methods often fall short in preventing PHI disclosures.
Post-Call Detection: Quality assurance typically identifies violations days or weeks after they occur, meaning the damage may already be done.
Sampling Limitations: Reviewing only a small percentage of calls (2-5%) leaves the vast majority of potential violations undetected.
Human Error in Monitoring: Quality assurance reviewers may miss violations or apply standards inconsistently due to lack of expertise.
Time Lag to Correction: Even when violations are detected, agents may continue making the same mistakes until they receive coaching.
Real-Time Compliance Prevention Technology
The Paradigm Shift:
Live assist technology represents a significant shift from traditional post-call reviews to real-time monitoring. This proactive approach ensures compliance during the call, preventing violations before they occur.
How Real-Time Prevention Works:
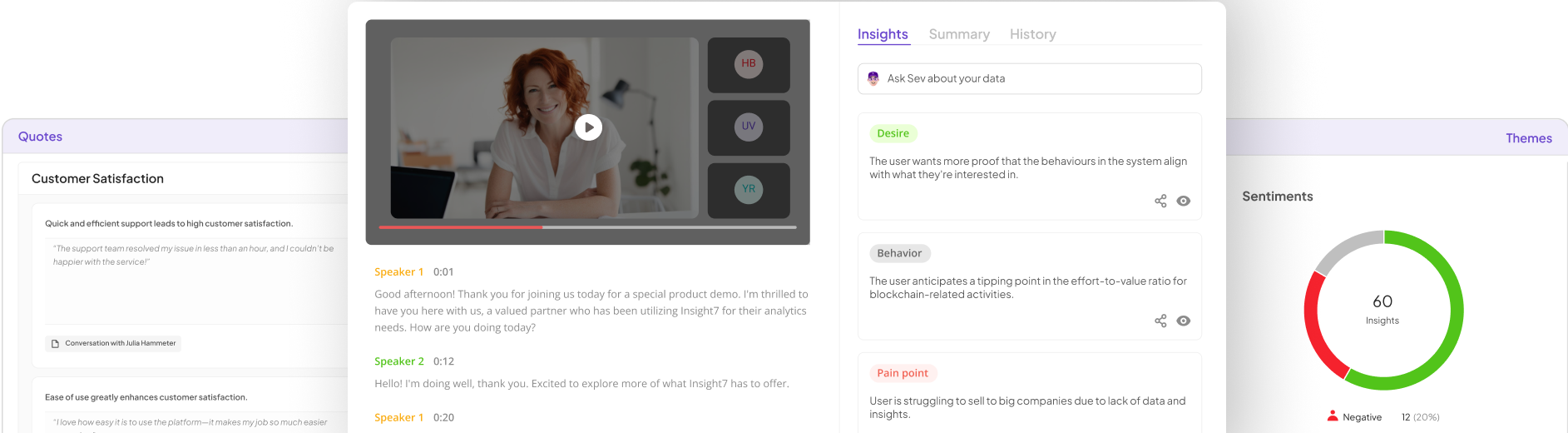
Detection Layer:
- Continuous speech-to-text transcription captures conversations in real time.
- Keyword and phrase detection identifies sensitive topics and potential violations.
- Context analysis helps determine the nature of the discussion, flagging any PHI-related inquiries.
Prevention Layer:
- Proactive alerts prompt agents to verify patient authorization before discussing PHI.
- Suggestions for compliant language guide agents on how to respond appropriately.
- Supervisor alerts can be triggered for serious violations, allowing for immediate intervention.
Documentation Layer:
- Automated logging captures compliance moments, creating an audit trail for regulatory readiness.
- Timestamp documentation ensures all disclosures are recorded accurately.
Scenario: Preventing Accidental PHI Disclosure
Scenario: A healthcare contact center agent receives a call from a family member inquiring about a patient's health status.
Setting: A busy healthcare contact center with multiple agents handling various patient inquiries.
Participants:
- Agent: A customer service representative trained in handling patient inquiries.
- Family Member: A caller requesting information about a relative's health.
Process:
- Call Initiation: The family member calls the contact center seeking information about the patient.
- Live Assist Activation: As the call begins, the live assist technology activates, monitoring the conversation.
- Detection of Sensitive Inquiry: The system recognizes the request for patient information and triggers an alert.
- Proactive Guidance: The agent receives a prompt: “HIPAA ALERT: Verify patient authorization before discussing PHI.”
- Verification Process: The agent is guided to ask specific questions to confirm the caller's identity and authorization.
- Blocking PHI Disclosure: If the caller cannot provide the necessary authorization, the system prevents any discussion of PHI until verification is complete.
Outcome: The agent successfully navigates the call without disclosing any unauthorized information, ensuring compliance with HIPAA regulations.
Compliance Monitoring, ROI & Platform Selection
Implementing live assist technology offers significant returns on investment by preventing costly violations.
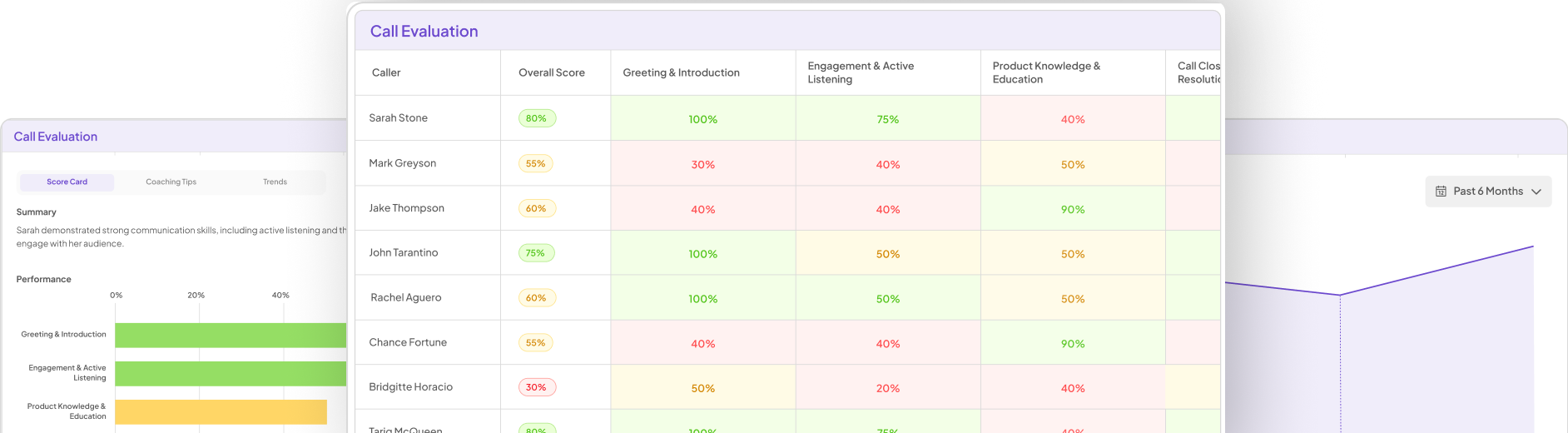
Real-Time Dashboards:
Supervisor View:
- Live compliance alerts for violations in progress.
- Agent compliance scores and disclosure completion rates.
- Violation prevention counts and risk-ranked agent lists.
Compliance Officer View:
- Organizational compliance metrics and regulatory adherence trends.
- Near-miss analysis to identify violations that were prevented.
- Audit-ready reporting for regulatory inspections.
ROI of Compliance Prevention:
Consider a healthcare contact center with 500 agents. If the system prevents 400 HIPAA violations annually, with an average fine of $10,000 per violation, the annual fine avoidance would be $4 million. If the platform costs $300,000 per year, the ROI would be 1,233%.
Technology Selection for Compliance:
When selecting a live assist platform, look for:
- Pre-built compliance rules for major regulations like HIPAA.
- Real-time violation detection and prevention capabilities.
- Comprehensive audit trails and regulatory reporting features.
- Custom compliance rules configuration to adapt to specific organizational needs.
By integrating live assist technology, organizations can enhance their compliance posture, protect sensitive information, and ultimately foster a culture of accountability and trust.