What’s the Most Secure Transcription Tool for Sensitive Conversations?
-
Bella Williams
- 10 min read
Secure transcription tools play a vital role in the modern digital landscape, especially when it comes to sensitive conversations. Imagine you are discussing critical business strategies or private personal matters; the last thing you want is for this information to be compromised. As industries increasingly rely on transcriptions, the urgency for secure solutions becomes paramount. This section will guide you through the essential features and options available for secure transcription.
In today's complex data environment, ensuring the confidentiality and integrity of spoken words is non-negotiable. By utilizing secure transcription tools, organizations can safeguard their sensitive discussions against potential risks and vulnerabilities. From encryption protocols to access management, understanding what each tool offers is crucial. As we delve into this topic, you'll discover how to select and implement tools that not only streamline your workflow but also prioritize the security of your most sensitive conversations.
Analyze & Evaluate Calls. At Scale.
Converting spoken words into written text has become a crucial component of many industries. However, when dealing with sensitive conversations, its essential to use secure transcription tools. This ensures the confidentiality and integrity of the information being transcribed. In this article, we explore the most secure transcription tools available for sensitive conversations.
Converting spoken words into written text has become a crucial component of many industries, particularly as organizations engage in more complex conversations. When discussing sensitive topics, however, the stakes are higher, making it essential to leverage secure transcription tools. These tools not only facilitate accurate text conversion but also protect the confidentiality and integrity of the sensitive information being transcribed. Thus, ensuring that any conversations involving personal data, proprietary business insights, or legal matters remain secure is paramount.
The need for secure transcription tools stems from various characteristics of sensitive conversations. From data breaches to unauthorized access, the potential risks require robust security protocols. Organizations should prioritize features like encryption, data privacy, and comprehensive access controls when selecting their transcription tools. In this article, we explore the most secure transcription tools available, helping you safeguard your conversations and maintain trust in your communication processes.
Why Secure Transcription Tools Matter
Secure transcription tools play a critical role in safeguarding sensitive conversations. When discussions involve confidential information or personal data, the risk of exposure can have significant repercussions. These tools employ advanced encryption methods to ensure that transcripts remain confidential and secure from unauthorized access. By using secure transcription tools, individuals and organizations can confidently engage in important discussions without fearing data breaches or potential misuses of their information.
Moreover, understanding the potential risks associated with unsecured transcription processes is crucial. Data breaches, unauthorized access, and unintentional sharing of sensitive content can lead to serious consequences, both legally and operationally. Implementing secure transcription tools mitigates these risks by providing features designed explicitly for enhancing security, such as access controls and regular security audits. Ultimately, prioritizing secure transcription tools is essential for maintaining privacy and trust in any communication that involves sensitive topics.
The Importance of Confidentiality
Confidentiality is the cornerstone of trust in any interaction involving sensitive conversations. When individuals share personal or proprietary information, the expectation is that it will be protected and used only for the intended purposes. Secure transcription tools play a vital role in safeguarding this information, ensuring that sensitive data remains confidential and inaccessible to unauthorized parties. By utilizing such tools, individuals and organizations can assure their clients and stakeholders that privacy is upheld at the highest level.
In today's digital age, breaches of confidentiality can lead to significant repercussions, including financial loss and reputational damage. Protecting conversations involving sensitive topics, like financial data or personal identifiers, is paramount. Secure transcription tools not only encrypt data during transfer but also provide controlled access to keep information safe. It is essential for users to prioritize confidentiality when selecting transcription solutions, as this will ultimately foster a secure environment for sharing vital information.
Confidentiality is paramount when dealing with sensitive data. In scenarios where business secrets or personal information are discussed, ensuring that this data does not fall into the wrong hands is critical.
When dealing with sensitive data, confidentiality is not just an option—it is paramount. In discussions involving business secrets or personal information, protecting this data from unauthorized access is critical. Secure transcription tools are designed to prioritize data privacy, providing a layer of security that helps to prevent sensitive information from falling into the wrong hands. These tools employ advanced encryption methods, ensuring that conversations are transcribed and stored securely.
Moreover, it is essential to understand the potential risks associated with unsecured transcription methods. Data breaches and unauthorized access can lead to significant repercussions, not just for the individuals involved but also for businesses and their reputations. Therefore, selecting a secure transcription tool that meets stringent compliance standards can mitigate these risks. By understanding both the importance of confidentiality and the potential vulnerabilities, organizations can make informed decisions when choosing the right secure transcription tools for their sensitive conversations.
Potential Risks and Vulnerabilities
Potential Risks and Vulnerabilities in secure transcription tools can jeopardize sensitive conversations. One major concern is data breaches, where unauthorized parties gain access to confidential information. Such incidents might stem from inadequate security measures, leaving transcripts vulnerable to hacking or misuse. Additionally, reliance on cloud-based services can introduce risks of service interruptions or data loss, which could compromise the integrity of sensitive discussions.
Another vulnerability involves user authentication. If robust procedures are not implemented, unauthorized users may gain access to confidential data. It is essential to ensure that only individuals with the proper permissions can access sensitive transcripts. Finally, inadequate encryption can allow intercepted data to be read by unauthorized entities. By understanding these risks, users can better appreciate the importance of choosing secure transcription tools, which actively mitigate these vulnerabilities through advanced security protocols.
Understanding the potential risks and vulnerabilities such as data breaches and unauthorized access highlights the need for implementing secure transcription tools.
Sensitive conversations often carry inherent risks, particularly data breaches and unauthorized access. When relying on traditional transcription methods or unsecure tools, these risks increase significantly. It is crucial to understand how easily sensitive information can be intercepted or mismanaged during transcription processes. This recognition highlights the urgent need for secure transcription tools designed to safeguard confidentiality, ensuring that sensitive data remains protected from potential threats.
Secure transcription tools use advanced encryption and access control mechanisms to protect data both in transit and at rest. By implementing these technologies, you not only mitigate the risks of unauthorized access but also enhance trust among stakeholders who rely on the integrity of their conversations. Investing in secure transcription tools is not merely a precaution; it is an essential step toward ensuring that information remains confidential and protected in an increasingly digital world.
Extract insights from interviews, calls, surveys and reviews for insights in minutes
Top Secure Transcription Tools for Sensitive Conversations
To effectively engage in sensitive conversations, utilizing secure transcription tools is vital. These tools not only convert audio into text but also ensure that the transcribed information remains confidential and protected from unauthorized access. When selecting a tool for sensitive conversations, it is essential to prioritize data security features, including encryption and access controls.
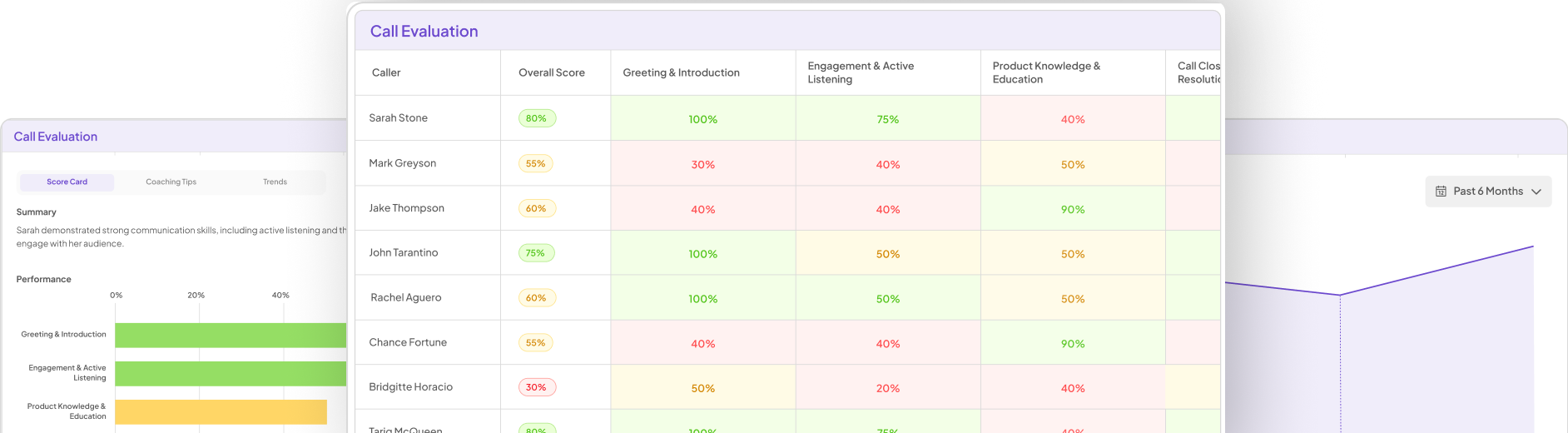
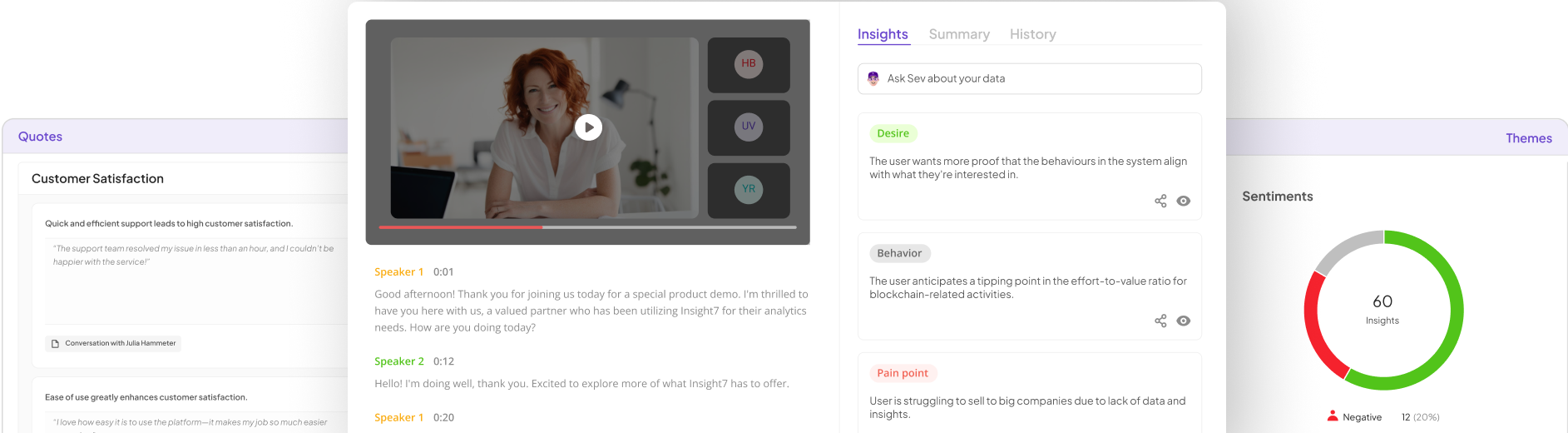
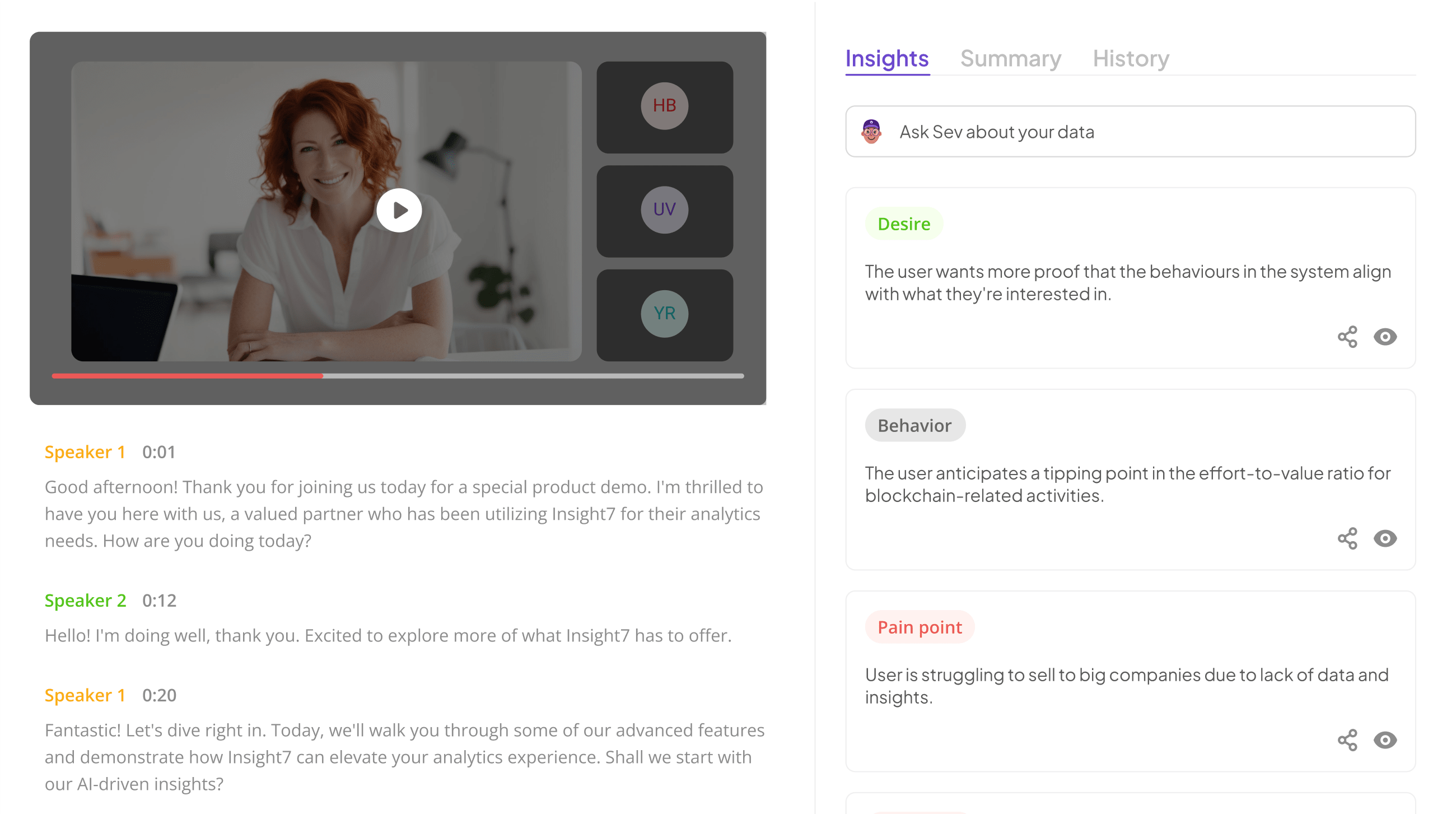
Several secure transcription tools stand out in the market. First, Insight7 provides top-tier encryption methods and secure access protocols, making it an excellent choice for safeguarding private dialogues. Next, Otter.ai stands out with its end-to-end encryption, ensuring transcripts are protected throughout the entire process. Trint also garners attention for its secure cloud storage capabilities, coupled with strong access controls that restrict unauthorized users. Similarly, Sonix emphasizes data privacy with its secure speech-to-text conversion features. Lastly, Happy Scribe balances accuracy and security, ensuring confidential transcriptions are protected adequately. By considering these tools, users can confidently engage in sensitive conversations while maintaining the integrity of their information.
To ensure maximum security, opting for the right transcription tool is crucial. Below is a list of the top tools known for secure transcription.
When it comes to the processing of sensitive conversations, selecting the right transcription tool is vital for maintaining confidentiality. Employing a secure transcription tool ensures that sensitive data is transcribed without risk of unauthorized access or data breaches. Awareness of the importance of security in transcription processes can be the determining factor in protecting private information.
The top secure transcription tools provide various features designed to safeguard data. For instance, some tools utilize advanced encryption methods to protect transcripts during the uploading and storage phases. Others focus on robust access protocols, ensuring only authorized individuals can view or edit sensitive content. This multifaceted approach to security not only reassures users but also builds trust in the transcription process, allowing for peace of mind while handling confidential information.
Insight7
Secure transcription tools play a crucial role in protecting sensitive conversations from various threats. When selecting the right tool, several key factors emerge that can guide users. Firstly, advanced encryption standards are essential to ensure data protection during transmission and storage. Secondly, user-friendly interfaces streamline workflows, allowing for efficient processing of information without compromising security. Finally, compliance with relevant regulations—such as GDPR—ensures that the tool aligns with legal requirements, providing an additional layer of trust.
In summary, assessing these elements helps users find the most suited secure transcription tool for their needs. By recognizing the importance of security features, they can make informed decisions that prioritize confidentiality. Ultimately, selecting a reliable transcription tool enhances both the security of sensitive conversations and the efficiency of information management. By prioritizing these criteria, users can safeguard their communications effectively.
Insight7 is recognized as a leading secure transcription tool, offering advanced encryption and secure access protocols to protect sensitive conversations.
When considering secure transcription tools, it is essential to prioritize those equipped with advanced encryption and secure access protocols. Such tools excel in safeguarding sensitive conversations from potential threats. The effectiveness of these transcription solutions lies in their ability to ensure that only authorized individuals can access the information, thereby maintaining confidentiality.
These tools employ state-of-the-art encryption standards, making data illegible to unauthorized users. Moreover, secure access protocols allow organizations to customize permissions, ensuring team members only see what they need to. This layered security not only protects the data during transmission but also while stored, addressing potential vulnerabilities. By utilizing these features, users can confidently manage sensitive discussions, knowing their information remains secure and private. Implementing a secure transcription tool thus not only protects data but also enhances organizational efficiency and trust.
Otter.ai
When considering secure transcription tools, one option stands out with its commitment to protecting privacy. It ensures that transcripts remain confidential through the use of end-to-end encryption. This robust security measure protects sensitive conversations from unauthorized access, a crucial feature for businesses handling confidential information.
Moreover, the platform integrates user-friendly features without compromising on security. Organizations can seamlessly convert discussions into text, benefiting from automated processing while ensuring that data integrity is preserved. With a focus on confidentiality, this tool addresses potential vulnerabilities often encountered in transcription services.
In summary, for a secure transcription solution, selecting a service that prioritizes data protection is vital. Keeping security at the forefront helps businesses maintain trust and confidentiality in their communications while navigating sensitive topics effectively.
Otter.ai utilizes robust security measures, including end-to-end encryption, to safeguard transcripts against unauthorized access.
Otter.ai employs comprehensive security measures, such as end-to-end encryption, to ensure the protection of transcripts from unauthorized access. This level of encryption works by encoding the data so that only authorized parties can access it, safeguarding the sensitive content of conversations. As information travels through various networks, the encryption ensures that it remains confidential, minimizing the risk of interception by malicious actors.
Furthermore, this security framework includes secure access protocols that help manage who can access the transcripts. Thus, users can feel confident knowing their sensitive data is kept safe from potential breaches. The combination of end-to-end encryption and strict access controls makes it a reliable option for those seeking secure transcription tools. In an era where data protection is critical, these measures are not just beneficial; they are essential for anyone handling sensitive conversations.
Trint
When considering secure transcription tools, the platform in question stands out for its dedication to data protection. With a focus on ensuring that sensitive conversations remain confidential, it implements advanced encryption methods and secure cloud storage. This commitment allows users to confidently transcribe discussions without worrying about unauthorized access to their data.
The platform provides robust access controls, which help monitor who can view and edit transcripts. By prioritizing user security, it positions itself as a vital player in the realm of secure transcription tools. Additionally, features enhancing user experience, such as intuitive interfaces and multi-device accessibility, contribute to its reliability. For organizations that prioritize data integrity, this transcription tool serves as an essential resource for maintaining privacy in sensitive conversations.
Trint offers secure cloud storage and strong access controls, making it a reliable choice for secure transcription tasks.
When it comes to secure transcription tools, ensuring data protection is core to maintaining privacy. One standout feature that enhances security is cloud storage, which allows for encryption and remote accessibility. This means sensitive transcripts are stored securely online, safeguarding them from physical access threats.
Additionally, strong access controls play a crucial role in protecting your data. These controls ensure that only authorized users can access specific files, significantly minimizing the risk of unauthorized viewing or sharing. Features like user permissions and two-factor authentication offer added layers of security, which are essential when handling sensitive conversations.
Selecting a tool that combines both secure cloud storage and robust access controls is vital for anyone tasked with sensitive transcription. This careful choice can lead to greater confidence in managing confidential information and maintaining compliance with data protection regulations.
Sonix
When considering the realm of secure transcription tools, one option stands out for its comprehensive approach to data privacy. It focuses on delivering secure speech-to-text conversion while prioritizing the protection of sensitive information. This tool is designed with advanced encryption protocols, ensuring confidentiality during every transcription process. Users can comfortably transform their conversations into written records without worrying about unauthorized access or data breaches.
Moreover, it enhances user confidence by implementing stringent access controls and providing transparency regarding data handling practices. For organizations dealing with sensitive conversations, adopting this secure transcription tool can significantly reduce vulnerabilities. In a landscape where information protection is paramount, this tool serves as a reliable choice for maintaining the integrity of confidential discussions, making it an invaluable asset for businesses and individuals who prioritize security.
Sonix provides secure speech-to-text conversion features with an emphasis on data privacy and security.
Secure speech-to-text conversion features are essential for anyone handling sensitive conversations. Conversations often contain confidential information that must be protected from unauthorized access. Recognizing this, leading transcription tools include robust security measures to ensure data privacy.
These secure transcription tools prioritize end-to-end encryption, ensuring that only authorized users can access transcriptions. Compliance with data protection regulations, such as GDPR, underscores their commitment to safeguarding personal and business information. Additionally, high-level security protocols guard against data breaches, reinforcing user trust in the platform.
When selecting a transcription tool, evaluating these security features is crucial. Understanding your unique security needs will guide you in choosing the most suitable option. With a focus on data privacy and security, these tools enable users to confidently transcribe sensitive conversations while minimizing potential risks. Thus, they play a critical role in maintaining confidentiality in today’s digital landscape.
Happy Scribe
When it comes to secure transcription tools, one option stands out due to its blend of accuracy and confidentiality. Happy Scribe provides users with an intuitive platform designed to handle sensitive conversations with care. The user-friendly interface allows individuals to upload audio files and quickly convert them into text format, all while ensuring the transcripts remain protected from unauthorized access.
Beyond just transcription, the platform offers advanced encryption standards, emphasizing the security of your data. Happy Scribe allows users to analyze transcriptions efficiently, pulling insights and highlights directly from the text. For those dealing with confidential information, choosing Happy Scribe as a secure transcription tool ensures conversations remain private and secure, safeguarding valuable insights from potential threats. By utilizing this tool, users can maintain control over their sensitive data while benefiting from accurate transcription services.
Combining accuracy with security, Happy Scribe ensures that transcriptions remain confidential and protected from potential threats.
Secure transcription tools not only strive for accuracy but also prioritize the confidentiality of sensitive conversations. Many organizations face the challenge of managing sensitive data effectively, which makes incorporating robust security measures essential. This ensures that transcriptions are both precise and protected from potential threats, such as data breaches.
Advanced encryption technologies play a crucial role in safeguarding the information processed by these tools. By implementing security protocols that prevent unauthorized access, users can confidently share sensitive audio files knowing that their content will remain confidential. Moreover, reliable transcription tools often include features such as secure cloud storage and strict access controls, further enhancing the security of sensitive conversations. In a world where data breaches are increasingly common, selecting a transcription tool that balances accuracy and security is vital for maintaining trust and safeguarding information.
Steps to Choose the Right Secure Transcription Tool
When selecting secure transcription tools, the process begins with understanding your specific security needs. Consider the types of sensitive conversations you will transcribe and the associated risks. For example, conversations involving personal information or proprietary business details may require stricter security measures. Identify whether you’re subject to any legal or regulatory requirements that further dictate your security standards.
Next, thoroughly evaluate the features and security protocols of potential transcription tools. Look for tools that offer strong encryption methods, secure access controls, and privacy policies aligned with best practices. Ensure that the tool provides reliable customer support and regular updates to maintain security against emerging threats. By taking these steps, you can confidently choose secure transcription tools that meet your needs and protect your sensitive conversations effectively.
Step 1: Identify Your Security Needs
Identifying your security needs is the first critical step in selecting secure transcription tools for sensitive conversations. Begin by evaluating the sensitivity of the data you handle. For example, are you transcribing confidential client meetings, internal strategy sessions, or personal interviews? Each scenario has different security demands that must be met to protect the information adequately.
Next, consider the regulatory compliance requirements relevant to your industry. Different sectors may impose specific data protection standards, such as HIPAA for healthcare or GDPR for companies operating in the EU. Understanding these regulations will guide you in determining the level of security necessary for your transcription needs. By clearly identifying your security requirements, you can confidently move forward in selecting a secure transcription tool that ensures confidentiality and protects against unauthorized access. Prioritizing your security needs will lead to better choices and safer conversations.
Determine the level of security required for your specific transcription tasks. Assess factors such as data sensitivity and regulatory compliance requirements.
To determine the appropriate level of security for your transcription tasks, start by identifying the sensitivity of the data involved. Sensitive information, such as personal details or confidential business strategies, demands strict safeguards. Similarly, consider the regulatory compliance requirements relevant to your field. Different sectors, including healthcare and finance, often have specific laws governing data handling and privacy that must be adhered to.
Next, evaluate the security features offered by various transcription tools. Look for options that provide encryption, secure servers, and robust access controls. By matching the security capabilities of these tools to your specific needs, you can ensure that your sensitive conversations remain protected. This thoughtful assessment will help you choose secure transcription tools that provide peace of mind while handling private information.
Step 2: Evaluate Features and Security Protocols
When evaluating secure transcription tools, a comprehensive review of their features and security protocols becomes essential. Start by examining the encryption methods employed by each tool. Robust encryption standards such as end-to-end encryption ensure that data remains confidential during transmission and storage. Additionally, assess user access controls; granular permissions can prevent unauthorized individuals from accessing sensitive information.
Next, consider compliance with industry standards and regulations. Tools that adhere to GDPR, HIPAA, or other relevant regulations demonstrate a commitment to security and privacy. Inspect how often the tool undergoes security audits and vulnerability assessments. Regular evaluations speak to the dedication of the provider in safeguarding user data and identifying potential weaknesses.
Finally, review user feedback and expert opinions on the reliability of the tool's security features. Collective insights can provide a clearer picture of how effective these transcription tools are in maintaining security. By thoroughly evaluating these aspects, you will be well-equipped to choose a transcription tool that meets your security needs.
Review the security features and protocols offered by each transcription tool to ensure they align with your privacy and security needs.
When you look into secure transcription tools, reviewing their security features and protocols is essential. Begin by assessing the encryption methods each tool offers. Strong encryption safeguards data during storage and transmission, preventing unauthorized access. Next, consider access controls. Features such as user authentication and permissions are vital for ensuring that only authorized personnel can access sensitive transcripts.
Moreover, check for compliance with industry standards like GDPR and HIPAA. These regulations ensure that the tools adhere to strict guidelines regarding data protection and privacy. Additionally, examine their data retention policies. A reliable transcription tool should allow users to manage and erase their data when necessary. By thoroughly evaluating these aspects, you can select a transcription tool that matches your specific privacy and security needs, ultimately ensuring that confidential conversations remain protected.
Conclusion on Secure Transcription Tools for Sensitive Conversations
In conclusion, selecting secure transcription tools for sensitive conversations is crucial for safeguarding confidential information. Ensuring that sensitive data remains protected involves understanding security features such as encryption and access controls. The right tool not only provides reliable transcription but also offers peace of mind that your conversations won't be compromised.
As you evaluate your options, prioritize tools that emphasize data privacy and security. By taking the time to analyze the available features, you can confidently choose a transcription solution that aligns with your specific security needs, ultimately enhancing the protection of sensitive information in your conversations.
Choosing the most secure transcription tool for sensitive conversations is essential in todays data-driven world. By understanding the importance of security and evaluating top tools, you can confidently select a solution that ensures confidentiality and protects sensitive information from potential threats.
In today's data-driven world, choosing the most secure transcription tool for sensitive conversations is imperative. The risks associated with data breaches and unauthorized access are ever-present, making it essential to prioritize security. Understanding your specific security needs is the first step in this process. Consider the type of sensitive information you handle, as well as compliance requirements that may apply to your industry.
Next, evaluate the features of potential tools. Look for secure transcription tools that offer robust encryption, data privacy measures, and strong access controls. Ensure these features align with your security requirements, enabling you to confidently protect sensitive information. When you find a tool that meets these criteria, you can trust that your conversations are transcribed with the utmost confidentiality, safeguarding your data against potential threats. By making a well-informed choice, you are one step closer to securely managing sensitive conversations.